Product Details
- The security concept is essentially based on a secure key store in which all keys are stored as if in a safe. From the outside, it is not possible to access those keys directly. This key store is contained in a security card (site key) and in each system component such as readers, standalone components and so on.
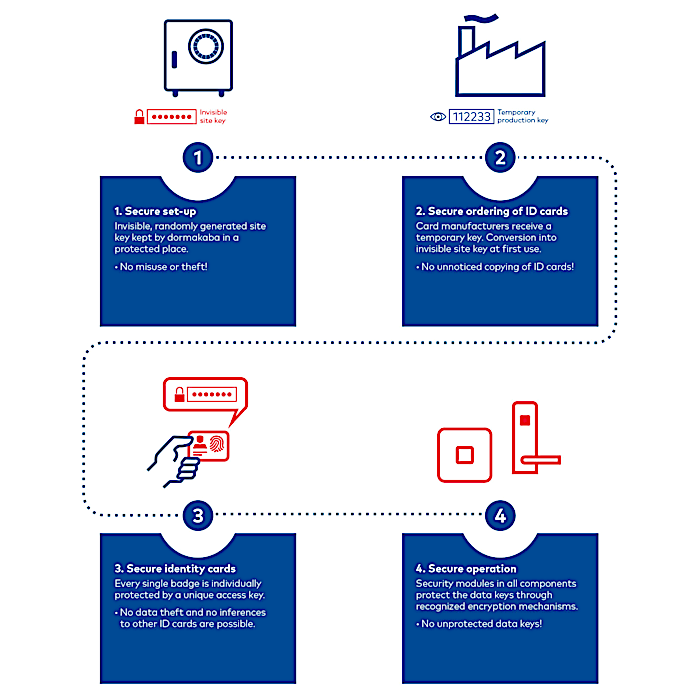
- Secure commissioning: Concealed site key, randomly generated by the system, which is stored by dormakaba in a protected location. This prevents misuse or theft.
- Secure ID card ordering: The ID card supplier only receives a temporary production key. Only when the new ID cards are delivered is this code converted into the concealed site key using a secure ARIOS-2 process. This process is logged in the system and means that no illegally produced ID cards can be used undetected.
- Secure ID cards: Each ID card is individually protected by a unique access key. No conclusions about other ID cards or data theft are possible.
- Secure operation: Security modules in all components protect the data key by recognised encryption mechanisms. In addition, the data exchange between the reader and the ID card is encrypted using the recognised AES or 3DES procedures. This protects against current common attack scenarios such as the so-called reverse engineering process or man-in-the-middle attack.
Applications
The ARIOS-2 security concept can be used for all dormakaba systems that work with MIFARE RFID media.


Product Downloads
- pdf
Technology brochure Secure MIFARE® RFID Solutions with ARIOS-2 by dormakaba
File description
380.17 KB
3.09.2024
The security concept for your MIFARE® Access Control system.
- pdf
We are happy to show you more
dormakaba Schweiz AG
Hofwisenstrasse 24
8153 Rümlang, Switzerland
Phone: +41 44 818 90 11
E-Mail: sales.ch@dormakaba.com



